Why institutional blockchain needs controlled visibility

Blockchain has a transparency problem, but not the one most people talk about. The problem is not that blockchains are transparent. Transparency is one of the most valuable properties a financial system can have. The problem is that on most blockchains, transparency is uncontrolled. Every balance, every transfer, every counterparty relationship is exposed to the entire network by default.
For institutions, that is not a feature. It is a barrier to adoption. We built Enygma to solve that problem properly: not by hiding everything from everyone, but by making transparency work like smart glass, clear when it should be clear, controlled when it should be controlled, and decided by the institution that runs the system rather than imposed by the network.

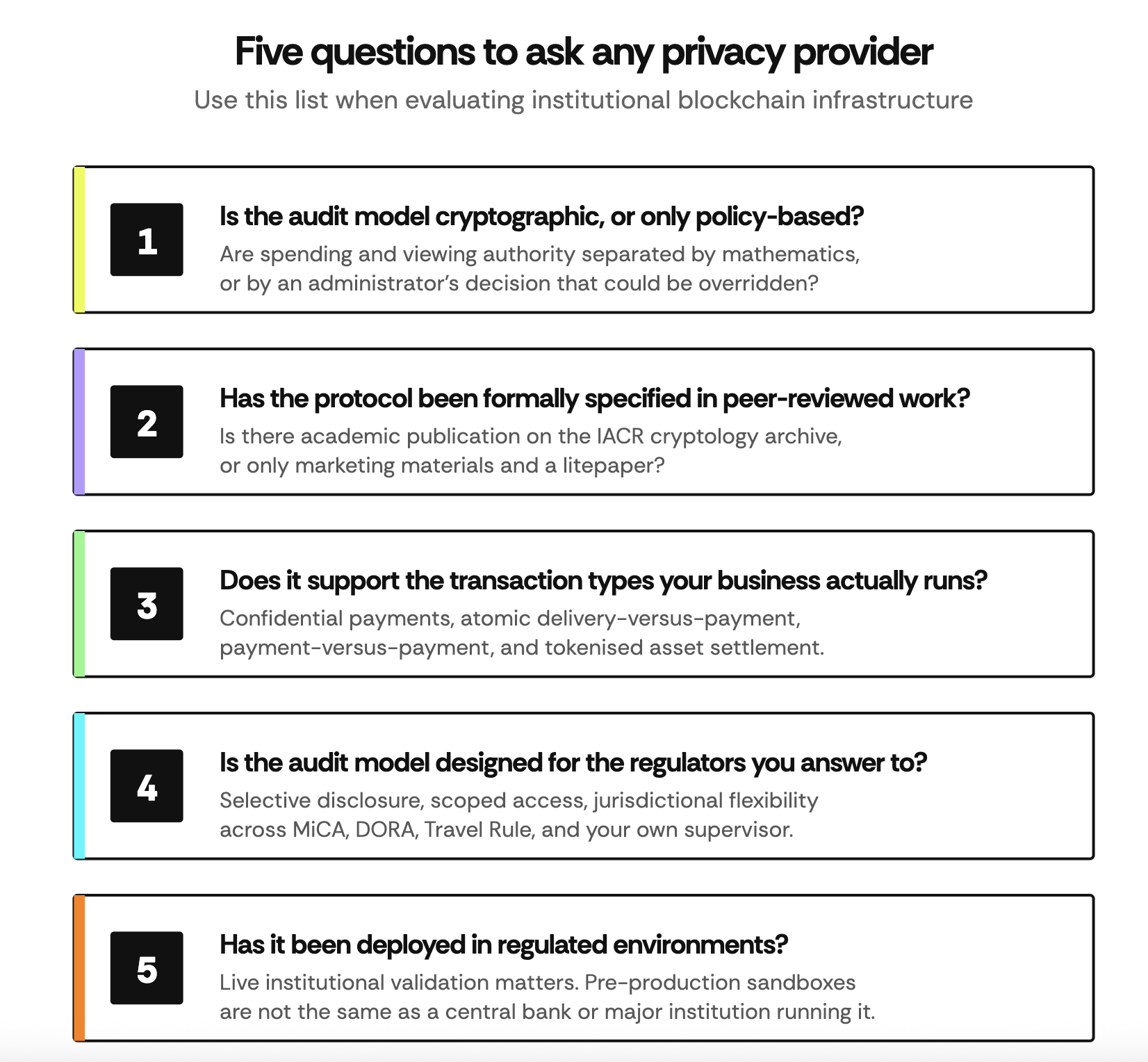
How institutions should evaluate privacy
If you are a regulated institution evaluating blockchain infrastructure, the question is not whether privacy matters; you already know it does. The question is whether the privacy you are being offered is real or a brochure claim.
The right test is simple.
What Enygma is, and what it is not
Enygma is the privacy framework of the Rayls stack. It enables confidential payments, atomic delivery-versus-payment and payment-versus-payment flows, and selective regulatory disclosure across a network of regulated institutions. It is built into the protocol itself, not bolted on as an external layer or moved off to a separate chain.
It is equally important to be clear about where Enygma's responsibility ends.
Enygma is not a compliance provider. KYC, KYB, sanctions screening, transaction monitoring, and regulatory reporting remain inside the regulated institution, on the institution's own approved stack. Regulated entities cannot delegate that boundary, and we do not move it.
Enygma is not a custodian. The institution holds its own keys, runs its own Privacy Node, and retains full sovereignty over its assets and its data.
Enygma is not a permissioned private chain disconnected from the public ecosystem. It runs on Rayl's infrastructure, which connects sovereign institutional environments to public chains where stablecoins, liquidity, and global counterparties already exist.
The institution decides, authorises, monitors, and reports. Enygma settles, protects, and provides verifiable evidence that the institution can map back to its own internal records.

How the privacy actually works
Privacy in Enygma is not a single feature. It is the result of several cryptographic primitives working together, each chosen because it solves a specific institutional problem.
Pedersen Commitments hide token balances on-chain while keeping them mathematically bound to their owner. The network can verify that inputs equal outputs in a transaction without ever seeing the numbers, and the issuer cannot freeze, inflate, or inspect balances without the holder's keys. Token sovereignty is cryptographic.
Zero-knowledge proofs validate every transaction. A payment is proved correct without revealing amounts, sender, or receiver. There is no trusted party that can break this guarantee.
Private tags allow recipients to detect incoming payments without exposing their addresses publicly. Anonymity is preserved at the receiving end as well as the sending end.
Homomorphic encryption supports programmable operations on confidential balances. This is what makes confidential delivery-versus-payment possible: the system can verify that both legs of a transaction settle atomically without either party seeing the other's position.
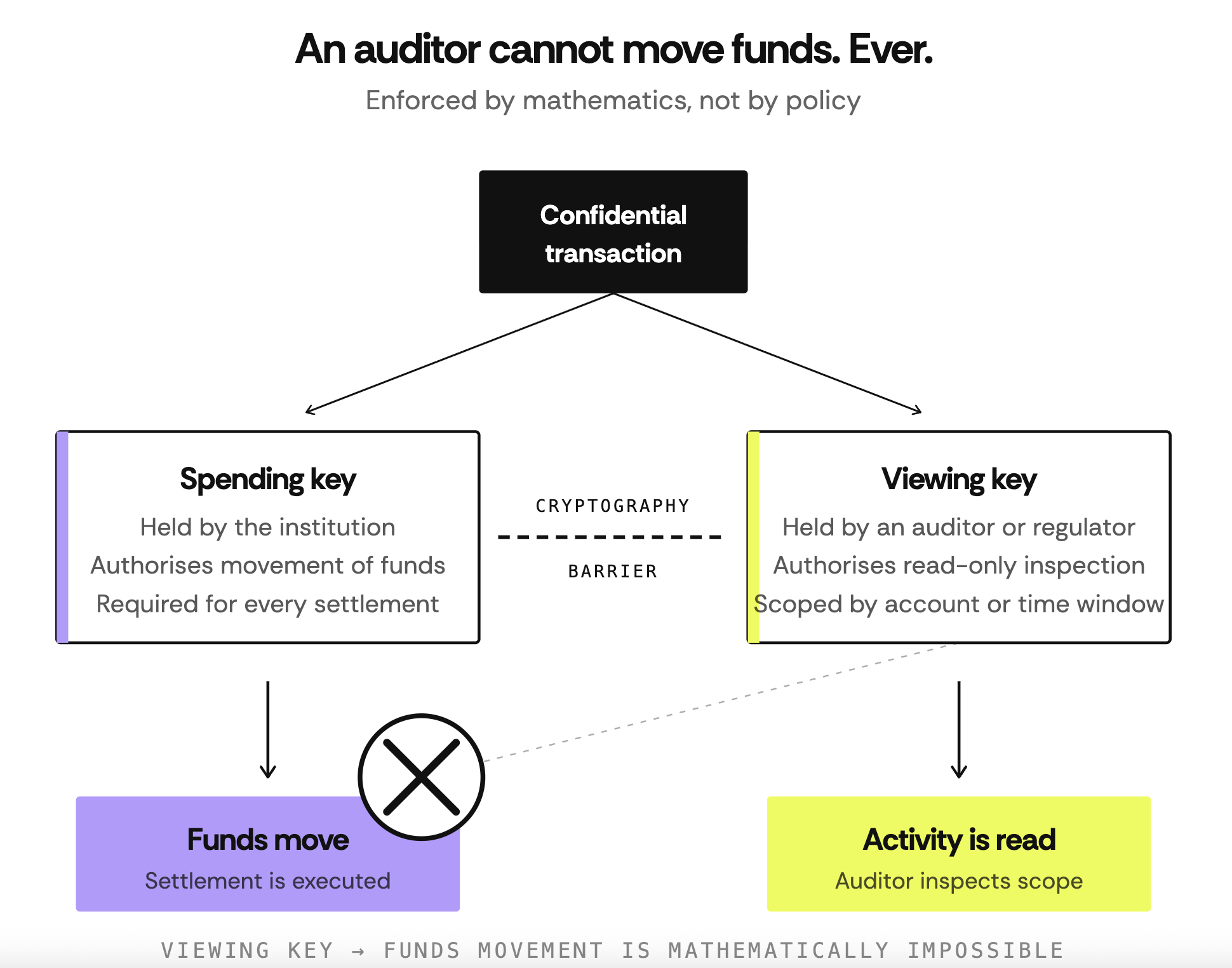
A cryptographic separation of spending keys and viewing keys gives the institution a precise tool for selective disclosure. An auditor or regulator can be given a viewing key scoped to specific accounts or specific time windows. They can inspect what they are entitled to inspect, and they cannot move funds under any circumstances. This is enforced mathematically, not by policy. It cannot be overridden by an administrator, a platform operator, or a compromised internal party.
Together, these primitives deliver what institutional privacy actually requires: confidentiality, anonymity, scalability, and auditability, all at once.
Privacy also has to hold up over time. Financial records remain sensitive for years after settlement, and a privacy model that depends only on cryptography, vulnerable to future quantum computers, has a built-in expiry date. Enygma is built with that horizon in mind. Five of its seven core cryptographic components are already quantum-resistant, including a NIST-standardised post-quantum key exchange. The remaining gap, in the zero-knowledge proof system, is an industry-wide one with no production-ready replacement available yet, and the Enygma protocol is designed to swap that component out the moment a viable post-quantum standard exists. This is the difference between privacy that protects today and privacy that will still protect a decade from now.
Where Enygma matters most
Privacy is not equally critical in every workflow. Three institutional use cases illustrate why Enygma was built the way it was.
Private payments and atomic asset exchange. When two institutions exchange tokenised assets across a multi-institution network, every detail of that exchange, the counterparties, the volumes, the timing, and the asset structure is commercially sensitive. On a fully transparent chain, that information leaks before settlement is complete. Enygma supports confidential transfers and atomic delivery-versus-payment using ERC-20, ERC-721, and ERC-1155 standards, with each institution keeping full data sovereignty on its own Privacy Node. Both legs settle atomically, or neither does, and no counterparty sees the other's position before execution. The outcome: institutions can transact with each other on shared infrastructure without giving up the confidentiality that competitive markets depend on.
On-chain FX and cross-border payments. Correspondent banking takes days, charges layered FX markups, and traps an estimated 27 trillion dollars globally in pre-funded nostro accounts. The information cost is also high: a bank's cross-border flows reveal its strategic priorities, client relationships, and liquidity positioning. Enygma enables a local-currency tokenised deposit inside a Privacy Node to be swapped on-chain for a public-chain stablecoin, with the cross-border leg encrypted and confidential, settling in seconds. The outcome: capital that was previously locked in nostro accounts is freed for productive use, and the bank's flow intelligence stays inside the bank.
Tokenised treasury management. Treasury operations consolidate deposits, credit exposures, and internal transfers across an institution. Exposing those flows publicly would reveal balance sheet structure, internal funding patterns, and counterparty relationships in real time. Enygma allows treasury operations to run on a sovereign Privacy Node with embedded compliance, real-time reconciliation, and T+0 finality, with optional public-chain bridging for global yield distribution when the institution chooses. The outcome: reconciliation cycles compress from days to seconds, and treasury teams gain programmable workflows without sacrificing the confidentiality their balance sheet requires.
In each of these cases, privacy is not an enhancement. It is the precondition that makes the workflow viable on blockchain at all.
Built differently, already deployed
There are other approaches to blockchain privacy. Some hide everything from everyone, removing the audit path regulators require. Some move privacy to a separate chain, breaking the trust and verifiability of public settlement. Some use encryption schemes where keys can be derived too easily. Some are technically sound but too computationally heavy to support institutional transaction volumes. Each solves one part of the problem. Enygma was designed to solve the whole problem, with cryptographic primitives chosen for each of the four properties of institutional privacy, an audit model that is enforced by mathematics rather than policy, and a protocol formally specified in two peer-reviewed papers on the IACR cryptology archive.
Rayls Enygma has not approached this as a branding exercise. The architecture has been specified in published academic work.
In Rayls: A Novel Design for CBDCs by Mario Yaksetig and Fan Xu
https://eprint.iacr.org/2025/1639 - The authors introduce Rayls as a CBDC-oriented design focused on privacy, high performance, and regulatory compliance, with Enygma enabling efficient anonymous transactions between banks.
In Rayls II: Fast, Private, and Compliant CBDCs by Mario Yaksetig et al.
https://eprint.iacr.org/2025/1638 - The design is extended and strengthened, with a more efficient Enygma model and a more explicit treatment of simultaneous privacy, scalability, auditability, and compliance.
It is not theoretical. Enygma has been validated in real-world use cases. This is why privacy is not a feature of the Rayls stack. It is the foundation that makes institutional blockchain adoption possible in the first place. That is why we built Enygma.
Subscribe to our newsletter





.png)